Intro

Cyberattacks rarely announce themselves with obvious warning signs. They usually begin quietly through a compromised password, a misconfigured system, or one careless click. By the time clear symptoms appear, attackers may have already moved deep into the network. Research highlighted by Squalio shows that many organizations take hundreds of days to detect a breach. That delay can mean prolonged, unauthorized access to sensitive systems and data. Advanced cybersecurity solutions aim to close that gap with earlier detection, automated response, and full endpoint visibility.
Why Faster Detection Changes Everything In Advanced Cybersecurity Solutions
Speed is not just a technical metric. It is the difference between a contained incident and a public breach notification.
When attackers gain access, they move fast. A recent report covered by TechRadar notes that automated scans now hit targets at a rate of 36,000 per second. That scale means exposed systems are discovered almost instantly. If detection on the defender’s side takes weeks or months, the imbalance is obvious.
Advanced cybersecurity solutions close that gap with real-time monitoring and behavioral analysis. Instead of relying solely on known malware signatures, they look for unusual patterns such as:
- Logins from unexpected geographies
- Privilege escalations outside normal workflows
- Large volumes of data leaving the network
These signals may seem minor in isolation. Together, they often form the earliest indicators of compromise.
The result is a dramatically reduced mean time to detect. And when detection happens early, response can begin before attackers entrench themselves deeper into the environment.
Real Time Monitoring And Intelligent Threat Detection
Modern attacks rarely rely on a single technique. They blend phishing, credential theft, lateral movement, and data exfiltration into a multi-stage process.
According to analysis from sources like McKinsey, organizations that adopt automated detection and response tools report measurable reductions in incident resolution time. That improvement matters because every hour counts once malicious activity begins.
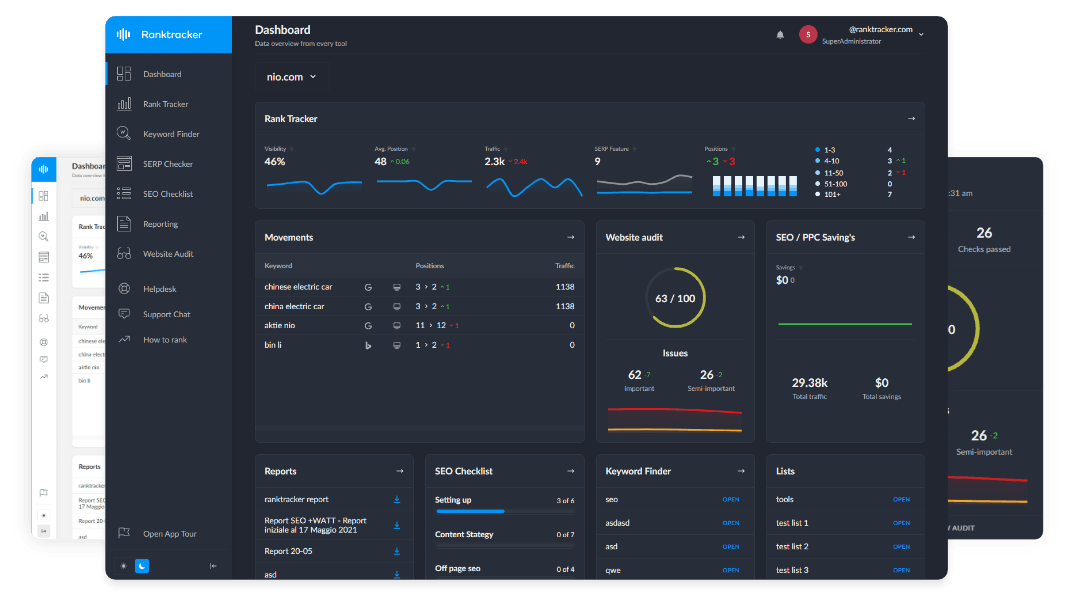
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
Real-time monitoring works by continuously collecting telemetry from endpoints, servers, and cloud workloads. Advanced analytics engines then evaluate that data against known tactics and suspicious behaviors. Instead of waiting for a manual review, automated alerts are triggered the moment risk thresholds are crossed.
Intelligent threat detection also reduces noise. Security teams are already stretched thin. If every minor anomaly triggers a high-priority alert, teams burn out and real threats slip through. Modern solutions prioritize context, correlating multiple signals before escalating an incident.
This approach strengthens both security and operational efficiency. Systems remain stable, sensitive data stays protected, and IT teams focus on genuine risks rather than chasing false positives.
How EDR Shrinks Response Time And Limits Damage
Endpoint Detection and Response, often shortened to EDR, plays a central role in advanced cybersecurity solutions. Endpoints are where users interact with systems, and they are frequently the first entry point for attackers.
Organizations that take the time to learn about EDR tools often discover how visibility at the device level transforms their response capabilities. With detailed telemetry from laptops, servers, and virtual machines, security teams can trace an attack from initial compromise through lateral movement.
This level of insight supports rapid containment. A compromised device can be isolated from the network in minutes rather than hours. Malicious processes can be terminated automatically. Suspicious files can be quarantined before they spread.
Businesses that implement EDR correctly report faster remediation and reduced breach impact. The practical benefit is simple: fewer systems go offline, fewer customers are affected, and fewer headlines are written.
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
EDR also supports forensic investigation. When leadership asks what happened, how it happened, and whether data left the environment, answers are backed by logs and evidence rather than guesswork.
Automation And AI In Advanced Cybersecurity Solutions
There is a lot of hype around artificial intelligence in cybersecurity. Some of it is justified.
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
Automation allows repetitive tasks such as log analysis and alert triage to run continuously without human intervention. AI-driven models help identify subtle deviations from normal behavior that traditional rule-based systems might miss.
Research cited by MoldStud indicates that organizations using automated threat detection resolve incidents significantly faster than those relying solely on manual processes. For a business owner, that translates to reduced downtime and lower recovery costs.
Automation does not replace human expertise. It augments it. Security professionals still make judgment calls, conduct investigations, and refine policies. The difference is that they are not starting from scratch each time an alert appears.
By combining automation with skilled analysts, advanced cybersecurity solutions create a layered defense that adapts to evolving threats without slowing down daily operations.
Building Resilience Through Advanced Cybersecurity Solutions
Advanced cybersecurity solutions focus on resilience, not chasing headlines. Rapid detection cuts attacker dwell time, while automated response removes costly delays. Clear endpoint visibility reveals what happened and limits impact. In a complex digital world, preparedness matters more than prevention alone. Evaluate your defenses and strengthen response capabilities now.