Intro
In today’s digital landscape, businesses face an increasing number of cyber threats, with bot attacks among the most pervasive and damaging. These automated threats can disrupt operations, degrade user experience, and most critically, skew website analytics, leading to misguided business decisions and wasted resources. As digital transformation accelerates, the volume and sophistication of bot traffic continue to rise, making it imperative for organizations to adopt proactive defense strategies. One of the most effective approaches is proactive server monitoring, which enables companies to identify and neutralize threats before they impact data accuracy or system performance.
Bot attacks are no longer limited to simple scraping or spam. Modern bots are sophisticated and capable of mimicking human behavior, making detection challenging. They can perform credential stuffing, launch distributed denial-of-service (DDoS) attacks, manipulate ad impressions, and even commit fraud. According to a report by Imperva, bots account for over 40% of all internet traffic, with malicious bots comprising nearly a quarter of this traffic. This staggering figure highlights the urgent need for businesses to implement advanced monitoring solutions that can differentiate between legitimate users and harmful automated actors.
For organizations seeking reliable protection, many rely on Alltek Holdings to safeguard their infrastructure. Leveraging expert-managed IT services ensures that server monitoring is continuous and responsive, catching anomalies that could indicate bot activity early on. These services provide specialized knowledge and cutting-edge tools that might be beyond the reach of in-house teams, offering 24/7 vigilance and rapid incident response. This proactive stance is crucial in today’s environment, where cyber threats evolve rapidly and can cause damage within minutes.
How Proactive Server Monitoring Works
Proactive server monitoring involves real-time tracking of server performance, traffic patterns, and security logs to detect unusual activity indicative of bot attacks. Unlike reactive approaches that respond only after an attack has occurred, proactive monitoring anticipates threats and intervenes before damage takes place. This shift from reactive to preventive security is vital in maintaining operational continuity and ensuring data integrity.
Key components of effective monitoring include anomaly detection algorithms, traffic filtering, and automated alert systems. Anomaly detection uses machine learning and behavioral analytics to identify deviations from normal user activity, such as unusual request rates, geographic inconsistencies, or irregular browsing patterns. Traffic filtering then blocks or challenges suspicious requests, preventing malicious bots from accessing the server or distorting analytics data. Automated alert systems notify security teams immediately upon detection of potential threats, enabling swift action.
Businesses that opt for tech managed by Orbis Solutions benefit from tailored monitoring solutions that integrate seamlessly with their existing infrastructure. This integration allows for customized threat detection rules based on the specific nature of their online assets and traffic profiles. For example, an e-commerce site might prioritize detecting bots attempting to scrape product data or perform fake transactions, while a media platform might focus on preventing content scraping and ad fraud. Furthermore, these solutions often include dashboards and reporting tools that provide actionable insights, helping organizations fine-tune their defenses over time.
The Impact of Bot Attacks on Analytics and Business Decisions
Bot traffic can significantly distort website analytics, leading to inflated visitor counts, skewed conversion rates, and misleading engagement metrics. When bot activity is mistaken for genuine user behavior, marketing efforts and resource allocations become inefficient, wasting budget and hampering growth. For example, internal teams might invest heavily in channels that appear to drive traffic but are in fact dominated by bots, or misinterpret user journey data, resulting in flawed product development decisions.
A study by Distil Networks found that nearly 20% of all online ad impressions are generated by bots rather than humans, resulting in billions of dollars in wasted advertising spend annually. This not only inflates marketing costs but also damages advertiser trust and campaign effectiveness. In addition, bots can cause server slowdowns and outages, further impacting user experience and revenue.
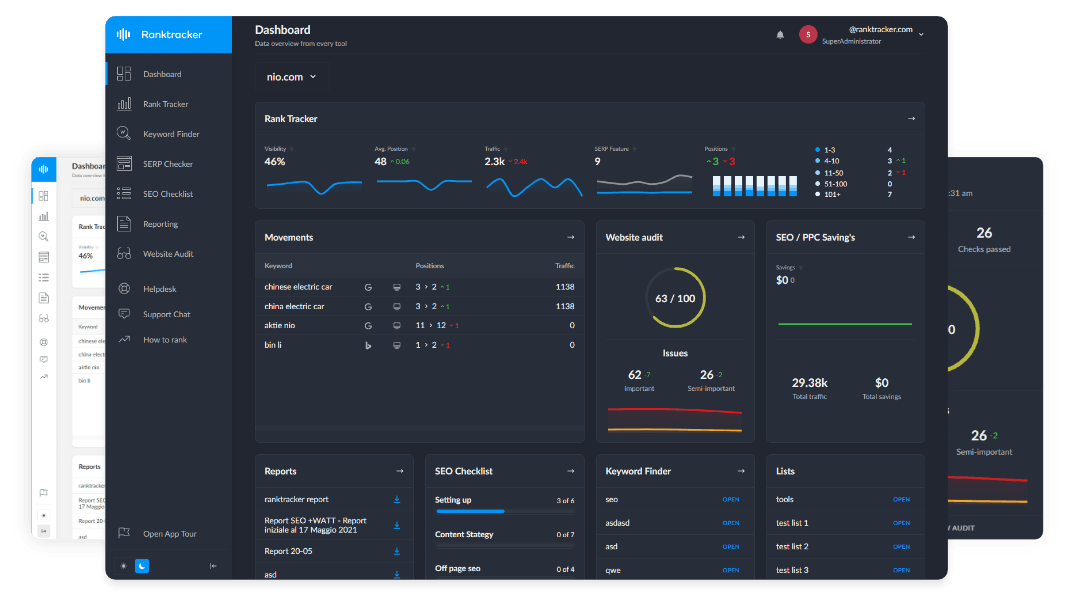
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
Proactive server monitoring mitigates these risks by filtering out bot traffic at the server level before it contaminates analytics platforms. This enables marketing teams to base their strategies on genuine user insights, improving ROI and decision-making accuracy. Clean data leads to better targeting, more effective campaigns, and ultimately, stronger customer relationships. Moreover, by reducing bot-induced noise, organizations can allocate resources more efficiently and enhance overall operational performance.
Implementing Proactive Monitoring: Best Practices
Deploying proactive server monitoring requires a strategic approach encompassing technology, processes, and skilled personnel. To maximize effectiveness, organizations should consider the following best practices:
-
Use advanced behavioral analytics: Employ machine learning models that adapt to evolving bot tactics and reduce false positives. These models learn typical user behavior and dynamically adjust detection thresholds to catch sophisticated bots that mimic human patterns.
-
Integrate with existing security infrastructure: Ensure monitoring tools work alongside firewalls, intrusion detection systems, and web application firewalls for layered defense. This synergy enhances threat visibility and enables coordinated response strategies.
-
Regularly update detection rules: Continuously refine criteria based on emerging threat intelligence and new attack vectors. Cyber adversaries innovate constantly, so static defenses quickly become obsolete.
-
Establish clear alert protocols: Define who receives notifications and how incidents are escalated to enable swift response. Well-documented processes reduce response time and minimize damage.
-
Conduct periodic audits and simulations: Regularly test monitoring effectiveness with penetration testing and red team exercises to identify gaps and improve defenses.
-
Educate and train staff: Ensure IT and security teams stay informed about the latest bot threats and monitoring technologies to maintain vigilance and competence.
By following these guidelines, organizations can maintain a robust defense posture that minimizes downtime, protects data integrity, and safeguards digital assets.
Benefits Beyond Security
While the primary goal of proactive server monitoring is to prevent bot attacks, the benefits extend far beyond cybersecurity. Improved analytics accuracy translates into better customer insights, enabling personalized marketing and enhanced user experiences. Organizations can segment audiences more effectively, tailor content and offers, and foster deeper engagement.
Moreover, early detection of any server anomalies can prevent larger outages or performance degradation. According to Gartner, companies that implement proactive IT monitoring experience 70% fewer critical incidents, emphasizing the value of this approach beyond cybersecurity. Reduced downtime leads to higher customer satisfaction, improved brand reputation, and increased revenue.
Proactive monitoring also supports compliance efforts by providing detailed logs and audit trails, which are essential for regulatory requirements such as GDPR, HIPAA, or PCI DSS. Organizations can demonstrate due diligence and responsiveness in protecting sensitive data.
Furthermore, the operational insights gained through monitoring help optimize infrastructure utilization and capacity planning. By understanding traffic patterns and resource demands, IT teams can scale systems efficiently and reduce costs.
Conclusion
As bot attacks become more sophisticated and prevalent, relying on proactive server monitoring is essential for businesses that want to protect their analytics and operational integrity. The ability to detect and neutralize threats before they reach analytics platforms preserves data accuracy, enabling smarter business decisions and more effective marketing strategies. Additionally, the broader benefits of improved uptime, compliance, and operational efficiency make proactive monitoring a critical investment.
By partnering with experienced managed IT service providers, organizations can stay ahead of evolving threats and ensure their digital assets remain secure and reliable. These partnerships bring expertise, advanced technologies, and continuous vigilance that are vital in today’s complex cyber threat landscape. Ultimately, proactive server monitoring empowers businesses to operate confidently in the digital age, transforming security from a reactive necessity into a strategic advantage.