Intro
Marketing agencies experiencing rapid growth face unique cybersecurity challenges that require immediate and strategic attention. As these businesses scale, they often handle increasing volumes of sensitive client data, including proprietary marketing strategies, customer information, and financial details. This accumulation of valuable data makes them attractive targets for cybercriminals, who continuously develop sophisticated tactics to exploit vulnerabilities.
According to a recent report by IBM, the average cost of a data breach in the marketing and advertising sector reached $4.35 million in 2023, highlighting the significant financial risks involved. Beyond the monetary impact, breaches can severely damage a company’s reputation and client trust, which are critical assets for marketing agencies operating in highly competitive environments.
To protect their assets and maintain client trust, high-growth marketing agencies must implement a robust cybersecurity framework. This involves not only investing in cutting-edge technology but also fostering a culture of security awareness among employees at all levels. One effective approach is leveraging specialized services like NetAccess's IT management, which provides tailored solutions to manage IT infrastructure securely and efficiently. These services can help agencies navigate the complexities of cybersecurity while allowing them to focus on their core marketing functions.
Essential Components of a Cybersecurity Checklist
1. Conduct a Comprehensive Risk Assessment
Before implementing any security measures, agencies should conduct a thorough risk assessment. This process involves identifying critical assets, potential vulnerabilities, and the likelihood of various cyber threats. Understanding these factors allows businesses to prioritize their cybersecurity efforts effectively and allocate resources where they are most needed.
A comprehensive risk assessment should include evaluating network architecture, data storage methods, third-party vendor security, and employee access levels. This holistic approach provides a clear picture of the agency’s security posture and helps in developing targeted mitigation strategies.
2. Implement Strong Access Controls
Access management is crucial in preventing unauthorized entry to sensitive systems. Agencies should enforce multi-factor authentication (MFA) across all platforms and ensure that employees have access only to the data necessary for their roles. This principle of least privilege minimizes the risk of insider threats and limits the potential damage caused by compromised credentials.
Utilizing services like The Computer Connection's IT management can help streamline this process by providing expert IT management and access control solutions tailored to the agency's needs. These managed services often include automated access reviews, real-time monitoring of login activities, and rapid response to suspicious access attempts, all of which strengthen the agency’s overall security posture.
3. Invest in Endpoint Security
With employees often working remotely or using personal devices, endpoint security becomes a critical line of defense. Installing comprehensive antivirus, anti-malware, and intrusion detection systems on all devices reduces the risk of breaches originating from endpoints.
Recent data shows that 70% of cyberattacks target endpoints such as laptops, smartphones, and tablets. This statistic underscores the importance of securing every device connected to the agency’s network, especially in flexible work environments that have become the norm.
4. Regularly Update and Patch Systems
Cybercriminals frequently exploit known vulnerabilities in software and operating systems to gain unauthorized access. Ensuring that all software is regularly updated and patched mitigates this risk. Automated patch management tools can simplify this task, especially for agencies managing multiple devices, ensuring that no system is left exposed due to outdated software.
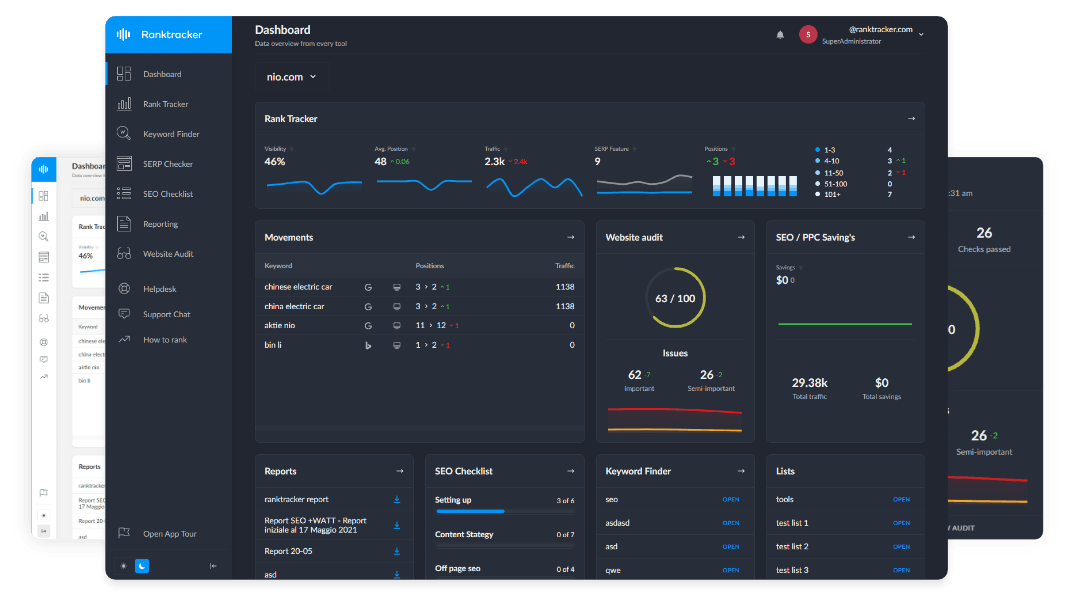
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
According to a report by Verizon, 60% of data breaches involve vulnerabilities for which patches were available but not applied. This highlights the critical importance of timely updates as a fundamental security practice.
5. Establish Data Encryption Protocols
Encrypting sensitive data both at rest and in transit ensures that even if data is intercepted or accessed without authorization, it remains unreadable. Encryption should be applied to emails, file transfers, stored client information, and databases. This layer of defense is essential for protecting intellectual property and personal data from unauthorized disclosure.
High-growth marketing agencies often exchange large volumes of data with clients and partners, making encryption a non-negotiable element of data security. Implementing end-to-end encryption protocols and secure communication channels protects the integrity and confidentiality of this data.
6. Develop an Incident Response Plan
Despite the best preventative measures, breaches can still occur. Having a detailed incident response plan enables agencies to act quickly to contain and mitigate the impact of cyber incidents. This plan should include clear roles and responsibilities, communication protocols, steps for containment, eradication, and recovery, as well as procedures for notifying affected clients and regulatory bodies if necessary.
Testing the incident response plan regularly through simulated exercises ensures preparedness and highlights any gaps that need to be addressed. A rapid and coordinated response can significantly reduce downtime and financial losses following a breach.
7. Train Employees on Cybersecurity Best Practices
Human error remains one of the most significant vulnerabilities in cybersecurity. Regular training sessions help employees recognize phishing attempts, use strong passwords, and follow security policies diligently. Cultivating a security-conscious workforce reduces the likelihood of successful attacks and promotes a proactive security culture.
A recent study found that 95% of cybersecurity breaches are caused by human error, emphasizing the critical role of ongoing employee education and awareness programs in risk reduction.
Leveraging Managed IT Services for Enhanced Security
Many high-growth marketing agencies lack the internal resources or expertise to manage complex cybersecurity demands effectively. Partnering with managed IT service providers offers a scalable and cost-effective solution. Companies like NetAccess Systems provide specialized services designed to protect growing businesses, including continuous monitoring, threat detection, incident response, and compliance management.
Statistics show that organizations using managed security services experience 50% fewer security incidents than those managing security in-house. This reduction is attributed to the providers’ ability to leverage advanced tools and experienced security personnel who stay abreast of evolving threats.
By outsourcing cybersecurity management, agencies can benefit from proactive defenses, 24/7 monitoring, and rapid incident response without the overhead of building an in-house security team. This partnership allows marketing agencies to concentrate on delivering value to clients while maintaining a strong security posture.
Compliance and Regulatory Considerations
Marketing agencies must also navigate various compliance requirements related to data protection, such as the General Data Protection Regulation (GDPR), the California Consumer Privacy Act (CCPA), and industry-specific regulations. Ensuring that cybersecurity measures align with these standards not only avoids legal penalties but also enhances client confidence.
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
Regular audits and assessments conducted by experienced IT management teams can help agencies stay compliant. For instance, offers compliance support as part of their managed IT services, assisting agencies in meeting regulatory obligations seamlessly. Compliance efforts should include documentation, employee training, and technical safeguards to protect personal and sensitive data.
Non-compliance can result in hefty fines and reputational damage. For example, GDPR violations can lead to fines of up to €20 million or 4% of annual global turnover, whichever is higher. Agencies that prioritize compliance demonstrate professionalism and respect for client privacy, which can be a competitive advantage.
Monitoring and Continuous Improvement
Cybersecurity is not a one-time project but an ongoing commitment. Agencies should establish continuous monitoring mechanisms to detect anomalies and respond promptly. Utilizing advanced tools like Security Information and Event Management (SIEM) systems can provide real-time visibility into network activity, enabling early detection of potential threats.
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
Moreover, periodic reviews of security policies and procedures ensure that the cybersecurity posture evolves in response to emerging threats. Engaging with experts such as those providing can facilitate continuous improvement through regular assessments, vulnerability scanning, and updates to security protocols.
Continuous improvement also involves staying informed about the latest cyber threats, participating in industry forums, and benchmarking security practices against peers. This dynamic approach helps agencies adapt to the rapidly changing threat landscape and maintain resilience.
Conclusion
High-growth marketing agencies must prioritize cybersecurity to safeguard their operations and maintain client trust. By following a comprehensive cybersecurity checklist that includes risk assessments, access controls, endpoint security, encryption, incident response planning, employee training, and compliance adherence, agencies can build a resilient defense against cyber threats.
Partnering with managed IT service providers like NetAccess Systems and The Computer Connection not only enhances security but also allows agencies to focus on their core competencies. As the digital landscape continues to evolve, proactive cybersecurity measures will remain indispensable for sustainable growth and success.
In the fast-paced marketing industry, investing in robust cybersecurity is no longer optional—it’s a business imperative. Agencies that adopt a strategic, layered security approach will be better positioned to protect their assets, uphold client confidence, and thrive in an increasingly interconnected world.