Intro
In today’s interconnected digital economy, businesses face an increasingly complex challenge: complying with a patchwork of global privacy laws while maintaining a smooth and efficient technology infrastructure. Regulations such as the European Union’s General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA), and Brazil’s Lei Geral de Proteção de Dados (LGPD) impose stringent requirements on how organizations collect, store, and process personal data. Failure to comply not only risks costly fines but can also damage a company’s reputation and erode customer trust.
The global landscape of privacy regulations is expanding rapidly. As of 2024, over 130 countries have enacted or are in the process of enacting comprehensive data protection laws, reflecting heightened public concern over personal data security. This proliferation of laws creates a complex compliance environment for multinational companies, which must navigate differing requirements based on jurisdiction.
According to a recent report, 92% of organizations worldwide view data privacy as a critical priority, yet only 45% are confident in their compliance efforts. This gap highlights the challenge of aligning legal mandates with existing technology stacks, which were often not designed with privacy compliance at their core. Moreover, the rapid evolution of privacy legislation demands agility from businesses that rely on legacy IT systems ill-equipped for swift adaptation.
Aligning IT Infrastructure with Privacy Compliance
One common pitfall for businesses is the mismatch between privacy compliance needs and their current IT infrastructure. Legacy systems may lack the necessary capabilities to support data minimization, encryption, or user consent management. This can lead to costly overhauls or the risk of non-compliance, which in turn can result in operational disruptions and financial penalties.
Engaging specialized services such as Edmonton managed IT can help organizations bridge this gap. Managed IT providers with expertise in privacy regulations can assess your current infrastructure, identify vulnerabilities, and implement tailored solutions. They ensure that data flows are traceable and secure, which is essential for meeting regulatory requirements. These providers often bring experience with integrating privacy compliance tools seamlessly into existing environments, minimizing downtime and technical conflicts.
For example, data minimization-an essential principle under GDPR-requires limiting personal data collection to what is strictly necessary. Legacy systems designed to collect and store large volumes of data indiscriminately often require reconfiguration or replacement. Managed IT experts can assist in redesigning data workflows to comply with these principles without compromising operational efficiency.
Investing in privacy-aware IT management also reduces the risk of operational disruptions. Poorly integrated compliance tools can cause system slowdowns or conflicts, potentially impacting business continuity. A managed approach ensures a harmonious balance between regulatory demands and technological performance. In fact, a survey found that 68% of IT leaders experienced increased system reliability after integrating privacy-focused infrastructure with expert assistance.
The Role of Cybersecurity in Privacy Compliance
Privacy laws not only govern how personal data is handled but also mandate robust security measures to protect this information from breaches. Cybersecurity frameworks must be aligned with privacy objectives, ensuring that data is shielded from unauthorized access or leaks.
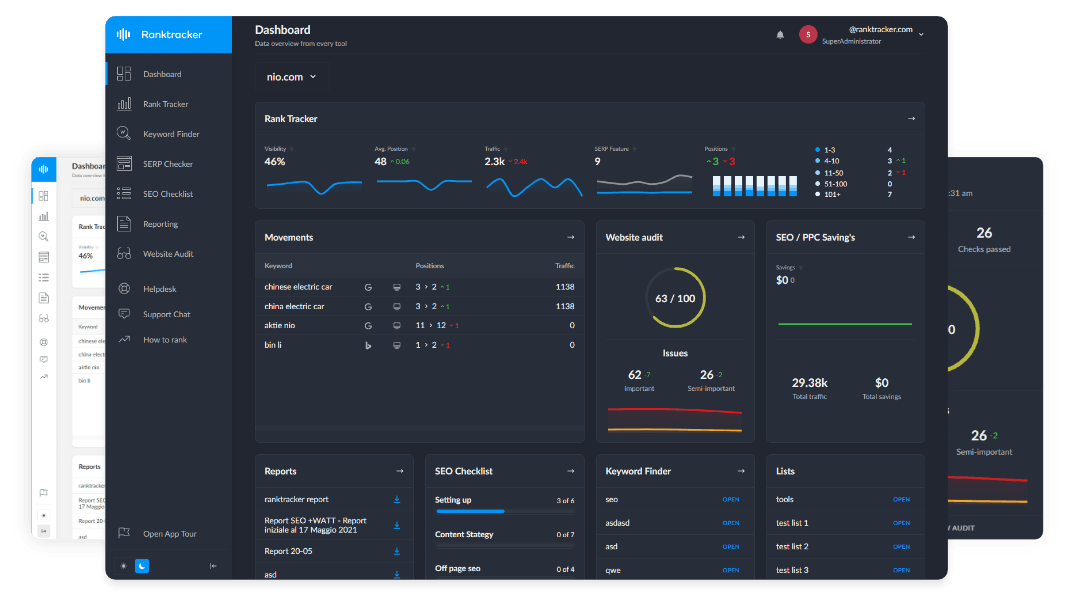
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
This is where NCC Data's cybersecurity approach plays a critical role. By adopting a cybersecurity approach that integrates privacy compliance, businesses can proactively defend against threats while adhering to legal standards. Their expertise enables the deployment of advanced security protocols, continuous monitoring, and rapid incident response capabilities.
The cost of data breaches continues to rise, with the average breach costing $4.45 million in 2023. Moreover, privacy violations can result in fines reaching up to 4% of global annual revenue under GDPR. These statistics underscore the importance of combining cybersecurity and privacy compliance strategies.
Beyond financial costs, data breaches erode customer trust and brand reputation. According to a report, 60% of consumers would stop doing business with a company following a data breach. Therefore, integrating cybersecurity measures that align with privacy laws is essential not only for compliance but also for sustaining long-term customer relationships.
Strategies for Seamless Privacy Integration
To avoid crashing your tech stack while navigating global privacy laws, consider the following best practices:
-
Conduct a Privacy Impact Assessment (PIA): Evaluate how personal data is collected, processed, and stored across all systems. This assessment identifies compliance gaps and informs necessary technology adjustments. PIAs also help prioritize remediation efforts and allocate resources efficiently.
-
Adopt Privacy-by-Design Principles: Integrate privacy considerations into the development lifecycle of applications and infrastructure. This proactive approach reduces retrofitting costs and enhances compliance. Embedding privacy controls from the outset ensures that new systems meet legal requirements without extensive rework.
-
Leverage Automation and AI: Automation tools can streamline consent management, data subject access requests (DSARs), and audit trails. AI-driven analytics can detect anomalies that may indicate privacy risks or breaches. For instance, AI-powered monitoring can flag unusual data access patterns that could signal insider threats or external attacks.
-
Centralize Data Governance: Establish clear policies and assign responsibility for data protection across departments. Centralized governance facilitates consistent compliance and efficient incident management. It also helps break down data silos that often complicate privacy oversight.
-
Train Employees Continuously: Human error remains a leading cause of privacy breaches. Regular training ensures staff understand their role in protecting personal data and complying with regulations. Training programs that include simulated phishing attacks and privacy scenario exercises have proven effective in reducing incidents.
Implementing these strategies requires coordination across IT, legal, and business units. Collaboration fosters a culture of privacy awareness and shared responsibility, which is critical for sustainable compliance.
Overcoming Common Challenges
Despite best efforts, companies often encounter obstacles when implementing privacy-compliant technology stacks. These include:
-
Data Silos and Fragmented Systems: Disparate systems may hinder unified data management, complicating compliance reporting and control. Integrating data sources through centralized platforms or data lakes can mitigate this issue but requires careful planning to maintain privacy safeguards.
-
Rapid Regulatory Changes: Privacy laws evolve frequently, requiring adaptive IT strategies. Staying current demands ongoing monitoring of legal developments and flexible technology that can be updated without extensive downtime.
-
Resource Constraints: Small and medium-sized enterprises may lack the expertise or funding to overhaul their technology. Managed services and cloud-based privacy solutions offer scalable options that reduce upfront investment and leverage external expertise.
Partnering with managed IT and cybersecurity experts can mitigate these challenges. Such collaborations provide access to specialized knowledge, scalable solutions, and ongoing support tailored to evolving privacy landscapes. Additionally, these partnerships can accelerate compliance timelines and reduce the risk of costly missteps.
The Business Benefits of Privacy Compliance
Beyond regulatory adherence, privacy compliance offers tangible business advantages. Building customer trust through transparent data practices can enhance brand loyalty and differentiate companies in competitive markets. According to a survey, 81% of consumers feel more confident purchasing from companies that prioritize data privacy.
Moreover, privacy-compliant organizations often achieve operational efficiencies through better data management and reduced risk exposure. Streamlined data governance can lead to faster decision-making and improved data quality, enabling businesses to respond more agilely to market demands.
Compliance can also open new market opportunities. Certain industries and regions require stringent privacy adherence as a prerequisite for partnerships or customer engagement. Demonstrating robust privacy practices can thus be a competitive differentiator and a driver of revenue growth.
Finally, companies with mature privacy programs report higher employee satisfaction, as clear policies and training foster a secure workplace culture. This can reduce turnover and improve overall organizational resilience.
Conclusion
Navigating global privacy laws without crashing your tech stack is a complex but achievable goal. Success requires a strategic blend of IT infrastructure optimization, cybersecurity integration, and ongoing governance. Leveraging industry experts such as can provide the necessary guidance and technical support to ensure compliance while maintaining business continuity.
As privacy regulations continue to evolve, companies that proactively adapt their technology and processes will not only avoid penalties but also build stronger, trust-based relationships with their customers, creating a sustainable competitive advantage in the digital age. Embracing privacy as a core business value rather than a compliance burden transforms risk management into an opportunity for innovation and growth.