Intro
Smartphones have become integral to our modern lives, with 60% of internet usage being viewed via smartphones.
Hence, mobile security has become essential for anyone who operates their day-to-day through a mobile device. Finding out how to know if your phone is hacked is now a necessary skill.
Luckily, there are simple, yet effective ways to prevent smartphone breaches. Let’s cut to the chase and dive into 10 tips to maintain security on your mobile device.
10 Tips To Ensure Your Smartphone Security
#1. Take precautions on public Wi-Fi
Public Wi-Fi is often hazardous, serving as a prime hunting ground for hackers. Password-free connections are commonly unencrypted, offering no base protection for those connected.
A common threat to public connections is man-in-the-middle attacks. A hacker creates their own imposter Wi-Fi, set up to look just like a public network. Once you’re connected, they wait to collect login credentials, payment data, and more.
What is a virtual private network?By using a Virtual Private Network (VPN), your browsing is fully disguised, even if connected to a fake network. VPNs encrypt your data, no matter the connection.
#2. Avoid public charging ports
Unfortunately, threats in public spaces don’t end on unsecured WiFi connections. Hackers can as well compromise shared charging ports in cafes, airports, or libraries. This method is colloquially known as “juice jacking”.
While the ports on your phone charge your device, they also transfer data. If a public charging port has been tampered with, you could be giving a hacker complete access to your smartphone and all the data within.
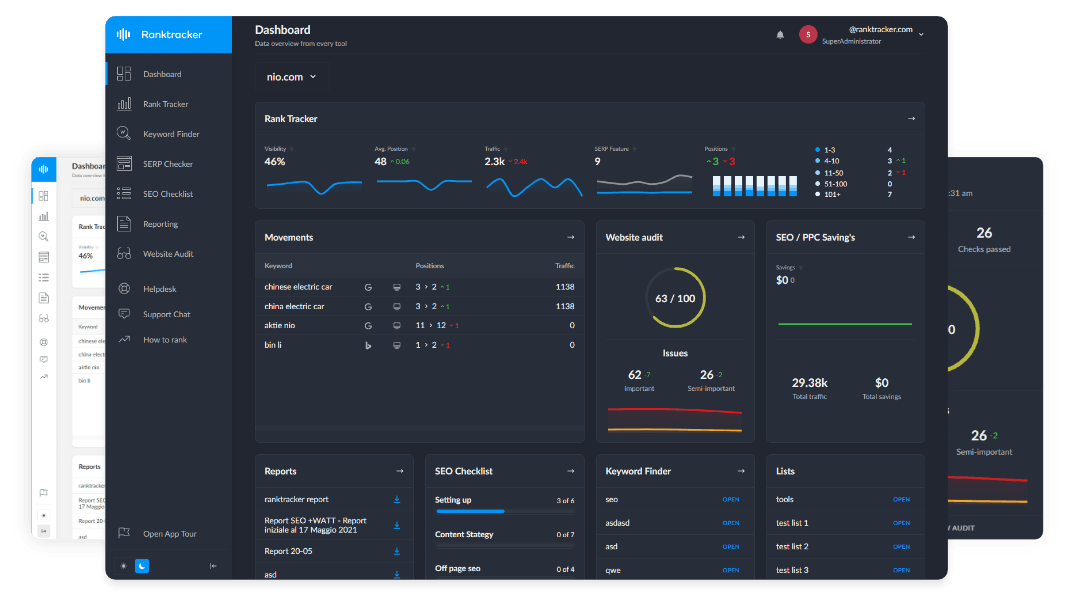
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
The best thing you can do is avoid these entirely. Opt for using your own wall charger, looking for standard power sockets instead.
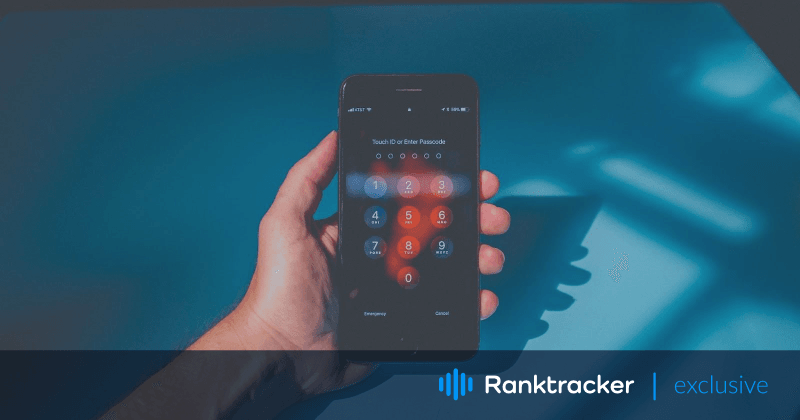
#3. Implement the built-in screen locks
Every smartphone offers screen locks, yet 28% of users report not using one. Cyberthreats are a huge concern, but physical theft is ever-present. A thief needs to steal your phone to have access to everything.
Screen locks come in the forms of:
- PIN code;
- Password;
- Pattern lock.
This doesn’t even include biometrics like facial recognition and fingerprint scanners. These can add an extra layer of personalized protection from phone thieves.
![]() (Source: 200degrees)
(Source: 200degrees)
#4. Enable remote tracking features
As mentioned, threats to your smartphone aren’t solely online. If physical theft happens, it’s not guaranteed that your screen lock will keep thieves out. In these scenarios, remote phone tracking features are your best ally.
Enable “Find My iPhone” (Apple users), or “Find My Device” (Android) in your phone settings. Not only will this allow you to track your device’s whereabouts, but also to remotely wipe the data, removing any private information.
#5. Make regular data backups
With all the preventative measures in the world, there’s always a chance of losing your valuable data. In the worst-case scenario, it’s essential to create comprehensive backups of the information you keep on your device.
When a phone is hacked, almost all data enclosed will become corrupted and unusable. Rather than starting from ground zero with a new device, a secure data backup will save you a tonne of effort and time.
#6. Upgrade your password security
Reusing passwords is a major security threat. A report found that out of 106 million users that had 2 or more passwords compromised, 60% reused passwords across their accounts.
I know what you’re thinking, how am I supposed to remember different passwords for every account I have? The simple answer is – you shouldn’t. Instead, opt for a password manager.
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
This software remembers and secures your login data for you. Most even offer password generators so you don’t need to come up with them yourself or worry about finding the saved passwords on Android or IOS.
#7. Keep your OS and apps updated
A core motivation behind a lot of updates is patching security holes. Over time, backdoors into old software become well-known to hackers. By avoiding updates, you may become a victim of cybercrime.
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
This equally applies to both your Operating System (OS) and apps. Fortunately, the fix is simple and easy to apply. Just keep your OS and apps updated at all times to take advantage of the latest security upgrades.
#8. Download apps only from official app stores
It may sound commonsense to some, but downloading apps from unofficial app stores can be dangerous. Malicious apps masquerade as interesting or already well-known games, but intend to infect your phone.
Stick to official app stores like Apple’s App Store and the Google Play Store. These marketplaces automatically scan software for viruses. If you’re an Android user, ensure your browser isn’t allowed to download apps from unknown sources. This can be done via the “Security” settings, on your phone.
#9. Audit your app permissions
Many app developers openly share your data with multiple third, and sometimes fourth parties. Worst of all, we give them permission to do so. If a third party becomes compromised, so does your data.
Auditing your apps’ permissions is a great way to stay on top of what data can be accessed on your phone. These can easily be found in your phone’s “Apps” settings. Revoke any permissions you see as unnecessary.
#10. Don’t “jailbreak” or “root” your phone
“Jailbreaking” (iPhone) and “rooting” (Android) your device removes the limitations imposed by mobile manufacturers. While this opens the possibilities and resources available to users, it comes with a major set of security risks.
Some of the attached risks include:
- Loss of inbuilt cybersecurity protections;
- Inability to access new security updates;
- Causing your device’s warranty to become invalid.
Jailbreaking and rooting allow administrator rights, but not just for the user. This means that when malicious code enters your phone, it will have unlimited access to all private information stored on the device.
Conclusion
Mobile security is vital in our increasingly digital world. By following these 10 tips, you’ll be safe from the vast majority of mobile security threats. With little effort, your private data will be untouchable by cybercriminals and thieves alike.