Intro
In recent years, telehealth has grown in popularity as it provides patients all over the world with easy access to healthcare services. However, as telehealth becomes more popular, strong security measures are required to guarantee patient privacy and safeguard sensitive data.
Understanding Telehealth Security
Vulnerabilities in communication channels
Technology and communication channels like messaging apps, video conferencing software, and internet connections are critical to telehealth. If these channels are not adequately secured, they may be open to cyberattacks, data interception, or unauthorized access.
Patient data breaches
Digital platforms are used to exchange sensitive patient data in telehealth. Personal health records, medical histories, and possibly financial data are included in this data. Hackers may target this data if it is not sufficiently protected. Effectively implementing telehealth services requires more than just secure technology—it demands a robust and user-friendly platform. The Updox telehealth platform ensures HIPAA compliance seamlessly, enabling healthcare providers to offer safe and efficient virtual care. From secure data transmission to encrypting video consultations, these platforms help protect patient privacy while providing essential medical services. This could result in data breaches and possible misuse of patient information.
Unauthorized access to patient information
Platforms for telehealth must make sure that patient data is only accessible to those who are authorized, such as patients and medical professionals. In the absence of appropriate authentication procedures and secure access controls, patient confidentiality and privacy may be jeopardized if unapproved parties obtain access to patient data.
Ensuring Privacy in Telehealth

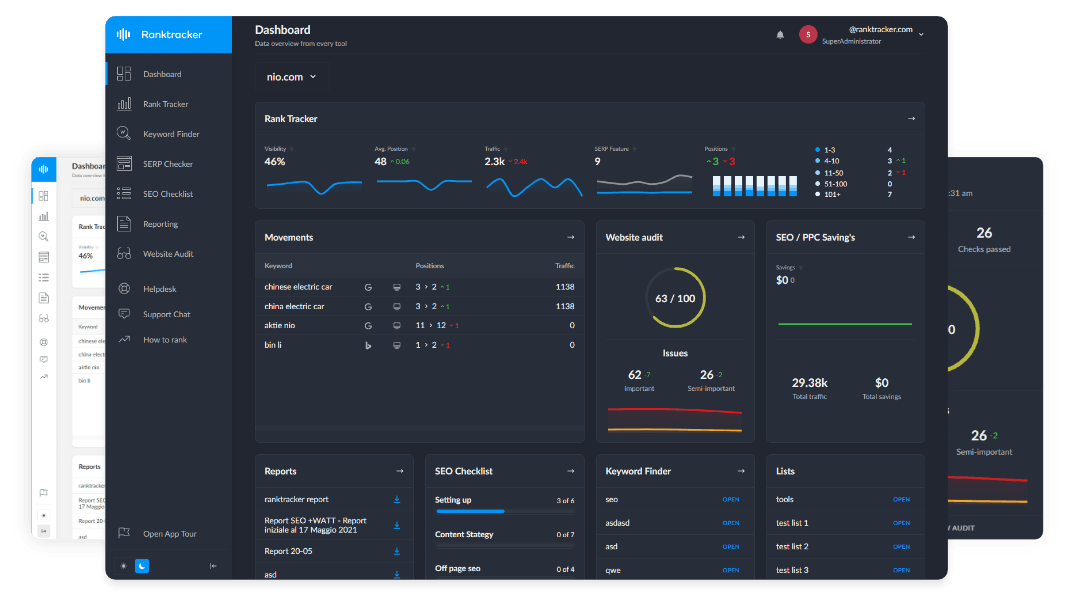
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
Implementing secure communication channels
1. Encryption of data transmission
Strong encryption protocols should be used by telehealth platforms to safeguard patient data integrity and confidentiality during transmission. Specialists need to encrypt data using algorithms that jumble the data. This makes it unintelligible to unapproved parties. Without the decryption key, data cannot be accessed or decoded even if it is intercepted during transmission.
2. Secure video conferencing platforms
Although video conferencing is an essential part of telehealth, security risks can also affect it. Healthcare providers should use secure telehealth video conferencing platforms like iotum with integrated security features to protect patient privacy. End-to-end encryption, safe login and authentication procedures, and the capacity to manage participant access and permissions are a few examples of these features.
Protecting patient data
1. Robust authentication and access controls
Telehealth platforms should implement strong authentication measures to verify the identity of users accessing patient data. This could involve the use of security tokens, biometric verification, or multi-factor authentication. Access controls should also be put in place to limit user access according to their role and the particular patient data they require access to. This lessens the possibility that unauthorized people will obtain sensitive information.
2. Regular data backups and disaster recovery plans
Telehealth platforms should create thorough disaster recovery plans and routinely backup data to prevent loss or damage to patient data. Frequent backups guarantee that patient data can be restored from a previous point in time in the event of a data breach or system failure. Plans for disaster recovery describe what should be done in the event of a natural disaster or security breach to protect patient information and maintain telehealth services.
Data Protection in Telehealth

Compliance with regulations and standards
1. HIPAA (Health Insurance Portability and Accountability Act)
A federal law in the United States called HIPAA establishes guidelines for safeguarding personal health information. Healthcare providers must make sure that patient data is safely transferred, stored, and accessible by authorized individuals in telehealth. Thus, specialists must put in place administrative safeguards like regular risk assessments and employee training on HIPAA compliance.
2. GDPR (General Data Protection Regulation)
The General Data Protection Regulation is an EU regulation that controls data privacy and protection. GDPR regulations must be followed by telehealth providers that operate in the EU or handle data belonging to EU citizens. This way, specialists must get patients' express consent before processing their data, make sure it's transferred and stored securely, and give people the ability to view, edit, and remove their data. A Data Protection Officer must be appointed by telehealth organizations, and data breaches must be reported within 72 hours.
Training and education for healthcare providers
1. Importance of proper handling and storage of patient data
Healthcare professionals should be made aware of the significance of handling patient data carefully. This means understanding how sensitive health data is and how patient confidence and privacy rights may be impacted by data breaches. Training should cover safe data entry, storage, transfer, and disposal methods in order to safeguard patient information. It should also emphasize the use of strong passwords, encryption, and secure communication channels.
2. Recognizing and reporting potential security incidents
Healthcare professionals should receive training on how to spot warning indicators of possible security incidents, like phishing attempts, suspicious network activity, and unauthorized access attempts. They ought to be aware of how crucial it is to notify the relevant IT or security staff members in their company as soon as possible of such incidents. Incident response protocols, such as how to lessen the effects of a breach, inform those who are impacted, and adhere to legal requirements to report the incident to regulatory bodies, should also be covered in this training.
Best Practices for Telehealth Security

Conducting regular security risk assessments
To find any holes or weak points in their systems, telehealth providers should routinely evaluate the security risks associated with their operations. They need to assess the possible risks, probability, and consequences of security breaches.
Engaging in third-party security audits
Telehealth providers ought to think about hiring outside specialists to carry out security audits. Thanks to these audits, specialists can give an objective evaluation of the security measures in place and assist in locating any holes or vulnerabilities in the system that may have gone unnoticed.
Employing strong password policies
Telehealth providers ought to impose stringent password policies requiring users to generate distinct and intricate passwords. This lessens the chance of password-related security breaches and helps prevent unwanted access to private patient data.
Establishing incident response plans
It is imperative for telehealth providers to establish clearly defined incident response plans in order to efficiently handle and minimize security incidents. These plans specify the protocols for communication, containment, and recovery that should be followed in the event of a security breach. A strong incident response plan helps safeguard patient data and reduces the harm that can result from a breach.
Conclusion*
Telehealth security is of utmost importance in ensuring privacy and data protection for both healthcare providers and patients.
While there are many advantages to the growing use of telehealth services, there are drawbacks as well, including the discovery of weaknesses that hackers could take advantage of. Healthcare companies need to put strong security measures in place, like encryption, multi-factor authentication, and frequent security audits, to mitigate these risks.
To avoid unwanted access and data breaches, healthcare personnel should also receive training on best practices for telehealth security.
Healthcare providers can reap the benefits of telehealth technology and ensure patient trust and confidence. They must prioritize telehealth security and take proactive measures to protect patient information.