Intro
Having a website is a great way to reach customers from all across the globe. Whether you have something to sell or information to share, the internet gives you an affordable opportunity to do so.
But, to make your site as successful as possible, you must ensure that it’s safe and protected from hackers. Hacking is a huge problem in 2022, with hundreds of incidents each week.
This article will explain how you can scare off hackers and make your website safe for you and your visitors.
Why do hackers target websites?
There are many reasons why hackers may target a website. And even though it often feels personal to the website owner, it usually isn’t. Hackers have a lot to gain from hacking a website, especially if it has a lot of visitors and hosts plenty of data. It’s also much less risky and easier to target smaller websites rather than big and complex websites of large organizations or governments.
Since many websites collect and store data from visitors, hackers have a huge incentive to obtain the data. They can then sell it on the dark web or use it to orchestrate further attacks.
Many websites also store intellectual property. If you’re running a business, you probably keep classified documents, vendor contracts, and other valuable files. Exposure of these files can lead to competitor advantage and reveal company secrets. This can have a financial and reputational impact on your business.
Even if you don’t store intellectual property or keep visitor data, your website can still be highly valuable to hackers. For instance, they can use it to host malware and spread it across the internet from your web server.
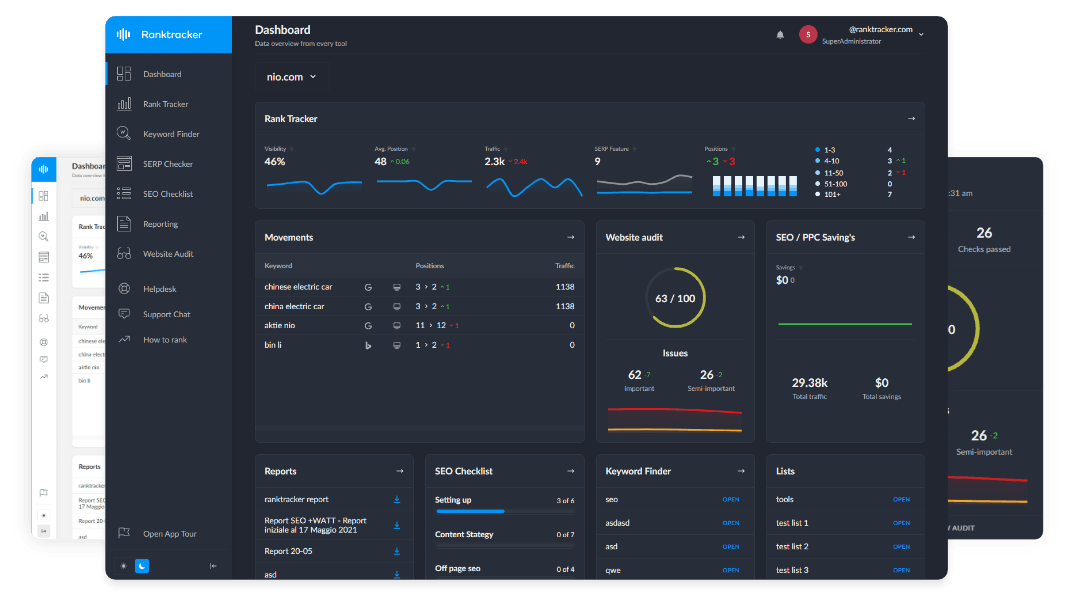
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
Last but not least, hackers can hack vulnerable websites for fun or to test and hone their skills. These attacks are usually less dangerous, as the attacker doesn’t have a clear goal. With that said, there’s no telling what they might do with whatever they discover on the website.
![]()
What are the most common website attack vectors?
An attack vector is how a hacker chooses to execute an attack on a website. Here are some of the most common attack vectors hackers use to breach websites:
Brute-force
Brute force attacks are simple and easy to execute but can be very effective. Hackers will try thousands of username/password combinations until they find the correct one. They will often automate the process with a bot, making it easy to test many combinations simultaneously. Adding two-factor authentication and setting a login attempt limit are effective ways to counter these attacks.
Social engineering
Social engineering attacks involve direct interaction with the victim. Attackers will attempt to obtain sensitive information directly from the victim by prompting them to take a specific action, usually while pretending to be someone else. The most common social engineering techniques are:
- Phishing
- Scareware
- Pretexting
- Baiting
Common sense is your best defense against phishing. If a message seems suspicious, do some digging before interacting with it.
SQL injections
Many websites use SQL to interact with databases. SQL is used for everything from logging a user in to storing data. A website becomes vulnerable to an SQL attack if user input isn’t protected with the proper filtering functions. Engaging in regular SQL practice can help developers identify and mitigate such vulnerabilities.
Hackers use tools to scan thousands of websites and test various injection techniques until they are successful. Successful attempts will allow hackers to access restricted sections of a website, add or delete content from the database, and more.
Cross-site scripting (XSS)
Cross-site scripting is an injection attack where hackers will try to inject malicious code into the website. The malicious code doesn’t usually affect the website, as it targets visitors directly. The code will run each time the visitor visits the website.
Once successful, hackers can see visitors’ sensitive information and cookies, and they may even be able to hijack their sessions. To prevent XSS attacks, your website must be able to validate input data and encode output data.
Denial of Service (DoS)
As its name suggests, a denial of service is a cyber attack where hackers will try to disrupt a website’s usual functions or make the website unavailable. The most common method of executing DoS is when the attacker tries to overload the website with traffic, causing it to crash or behave abnormally.
Distributed denial of service (DDoS) is a more advanced version of this attack. It utilizes botnets - a series of infected machines, to carry out large-scale attacks. The attack is way more powerful when multiple devices target a single victim. Hackers can either build up their own botnets or rent them from other attackers when needed.
![]()
Securing your website from hacking incidents
Now that you know the reasons behind website attacks and the most common attack methods, let’s look at some ways you can protect your website:
SSL certificate
Unless your website is old and outdated, it’s probably already running on HTTPS and has an SSL certificate.
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
An SSL certificate encrypts the data transfer between the website and the visitor’s browser. It protects a customer’s transactional data and other valuable visitor information. You can tell whether your website is SSL protected if it has a padlock icon next to its URL.
SSL certificates usually come as part of the website installation package or as an additional purchase for a small fee. You can also purchase them separately.
Use strong passwords
Brute force attacks can only be effective if your passwords are common or easy to guess. With a strong password that incorporates numbers, lower and upper case letters, and special characters, it will be impossible for hackers to get through, even if they’re using bots to automate the process.
If you’re afraid you will keep forgetting your password, use a password manager. A password manager will not only store your password securely, but you can also use it to generate strong passwords.
Keep software up to date
Software updates are crucial in addressing vulnerabilities and thus in keeping your website safe. This includes updates to the server operating system, a CMS, forum, or any other software your website is running.
You can even use detection tools to notify you whenever they find a vulnerability in some of your software.
If you have any plugins installed, update those as well. You can enable automatic updates for plugins, but that may cause issues if the update is incompatible with the website version.
Limit file uploads
Allowing users to upload files to your website can be a significant security risk. Hackers can easily fake file extensions. What appears to be a .jpg file can be .php and execute a harmful script on your server. Even if it’s indeed an image, hackers can hide the script in the image’s comment section.
Depending on what your site is about, it may be difficult to block file uploads altogether. Still, there are things you can do to prevent malicious files from entering.
The All-in-One Platform for Effective SEO
Behind every successful business is a strong SEO campaign. But with countless optimization tools and techniques out there to choose from, it can be hard to know where to start. Well, fear no more, cause I've got just the thing to help. Presenting the Ranktracker all-in-one platform for effective SEO
We have finally opened registration to Ranktracker absolutely free!
Create a free accountOr Sign in using your credentials
One option is to automatically change the file name upon uploading to ensure it has the correct extension. You can also add code to change file permissions. That way, users can only upload certain file types. The safest solution is to store all files outside the webroot folder.
Utilize website security tools
Website security software can perform automated security scans on your website to detect vulnerabilities, also known as penetration tests.
There are many free pen-testing tools out there. They will simulate exploits and attacks that hackers would use to detect any vulnerabilities.
Results from these testing tools can be daunting and include hundreds of possible vulnerabilities. You will find that most of them won’t apply to your site and what you’re doing. Mainly focus on addressing the critical issues. The tool will explain the vulnerability and how it can be exploited. Some tools even provide guides for fixing the vulnerability. When managing incident responses triggered by these scans, exploring pagerduty alternatives can help streamline alerting and resolution workflows for your team.
Final thoughts
Whether you’re a business storing valuable data on your website or have a small blog you run as a hobby, keeping your website secured should be a top priority. Hackers target websites for many reasons. They are usually financially motivated, but some do it for fun or to hone their hacking skills.
Knowing the most common attack vectors can help you address some of the main concerns regarding website security. After implementing what you’ve learned from this article, run some free security scanning tools through your site to identify any remaining security threats.